#sponsored
More than 40% of all emails sent are spam or potentially harmful, such as phishing or malware. So, to keep our inboxes clean and our systems free of viruses, we need to filter incoming emails. And this needs to be done before the malicious email reaches our end users.
This is where Exchange Online Protection (EOP) comes is in. EOP is the cloud-based mail filtering service from Microsoft 365. EOP is included in all Microsoft 365 plans that come with Exchange Online—and the good news is, it’s enabled by default.
So what exactly does EOP filter and how do you configure it? And what third-party options are available to protect your mail?
How does Exchange Online Protection work?
All incoming (and outgoing) mail is processed through EOP. All the mail undergoes four different steps to filter out any malicious mail that we don’t want to receive.
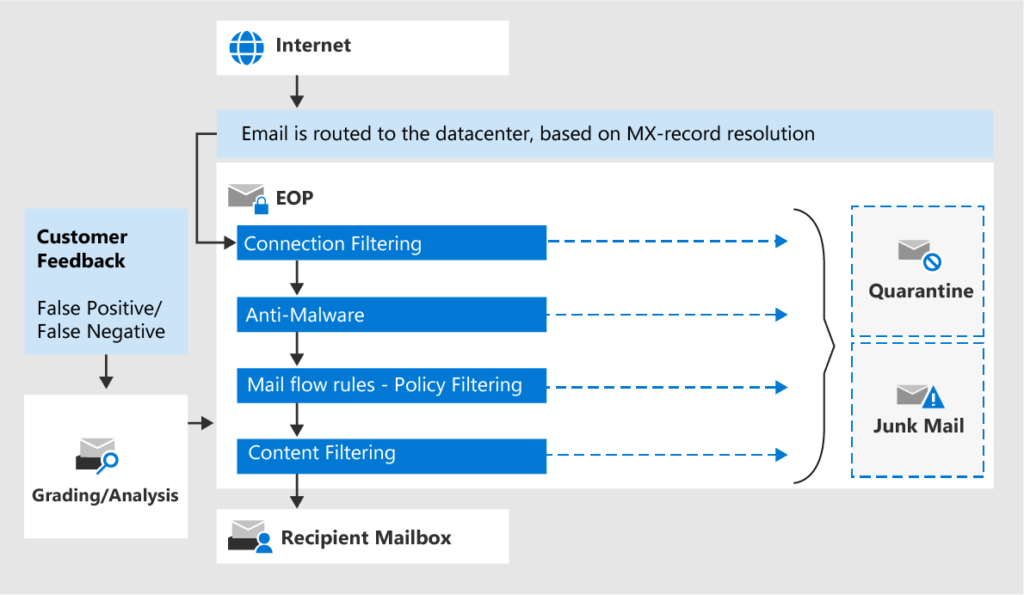
Connection Filtering
The first step is connection filtering. This will check the sender’s reputation, based on the sender’s IP address, to filter out most of the unwanted emails. You can use the connection filter in Exchange Online to block additional IP addresses.
Anti-Malware
The next step is to scan the emails for malware. EOP uses the anti-malware policy that we can configure in the security center to scan for potential harmful messages/attachments and quarantine the emails.
Mail flow rules
The mail is then processed through your mail flow rules. Mail flow rules can, for example, warn the recipient of potentially harmful messages based on keywords or block all attachments to the info mailbox.
Content Filtering
The last step is content filtering. Mail is evaluated based on the anti-spam and anti-phishing policies. Harmful messages are identified as spam, phishing, or spoofing with the appropriate confidence score.
You can configure what actions should be taken, such as quarantine, mark as junk mail, send an alert, etc., within the anti-spam and anti-phishing policies.
Setting up EOP
Securing your Office 365 tenant is important but often forgotten. To mitigate this, Microsoft has enabled many security features by default. This ensures that most Exchange Online environments are protected at a base level.
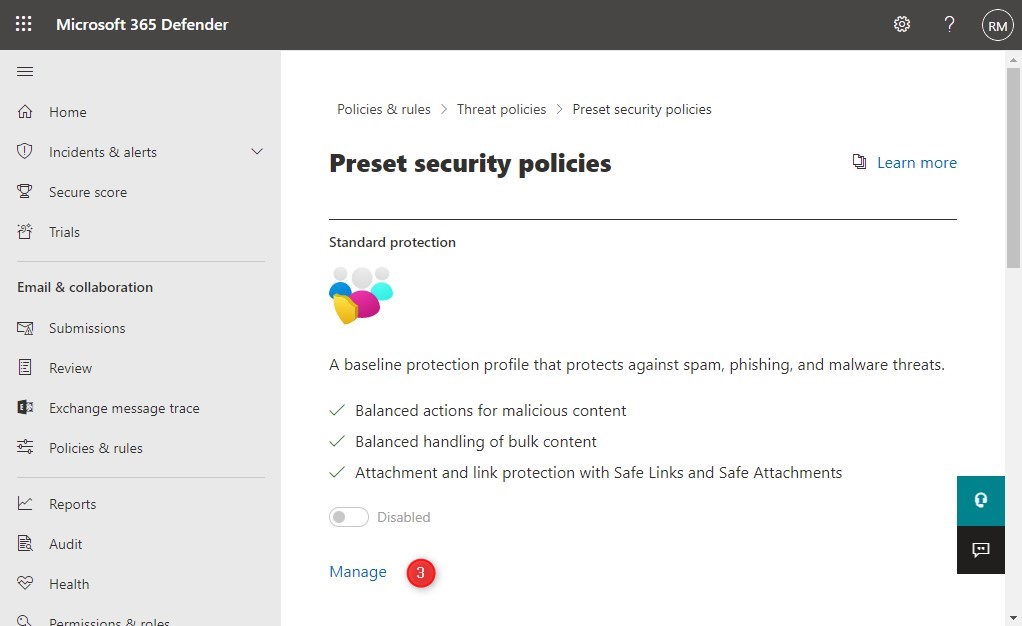
If you have a new tenant, then the best way to set up EOP is to start with one of the preset security policies:
- Open the Microsoft 365 Security Center
- Navigate to:
- Policies & Rules
- Threat Policies
- Preset Security Policies
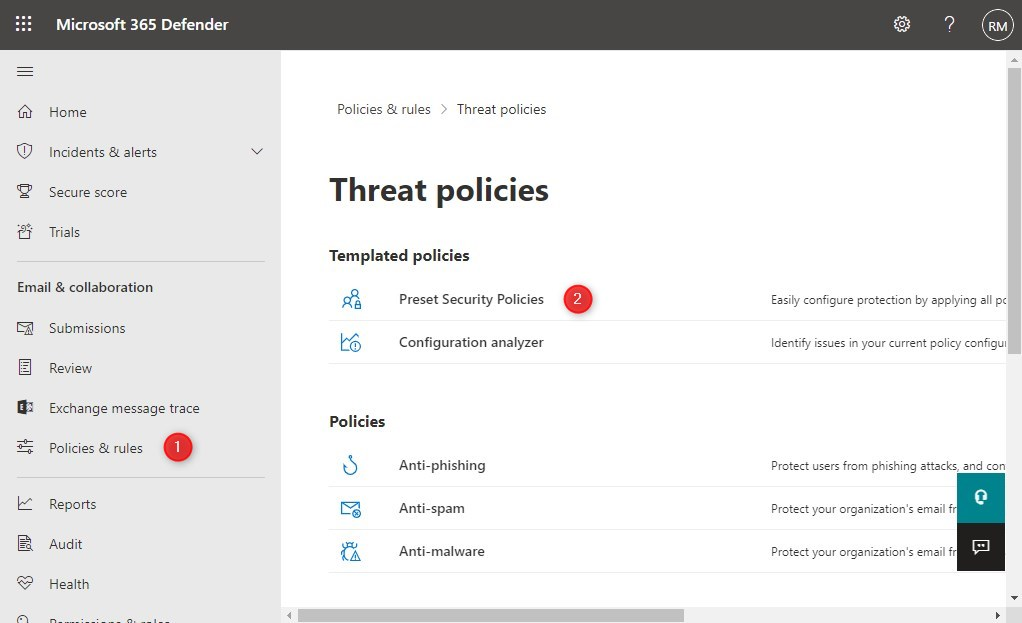
- Click Manage to enable the Standard Protection policies
- You can test the policy to a select group of users or enable it for your entire domain. Type your domainname to apply the policy to the whole tenant and click Next.
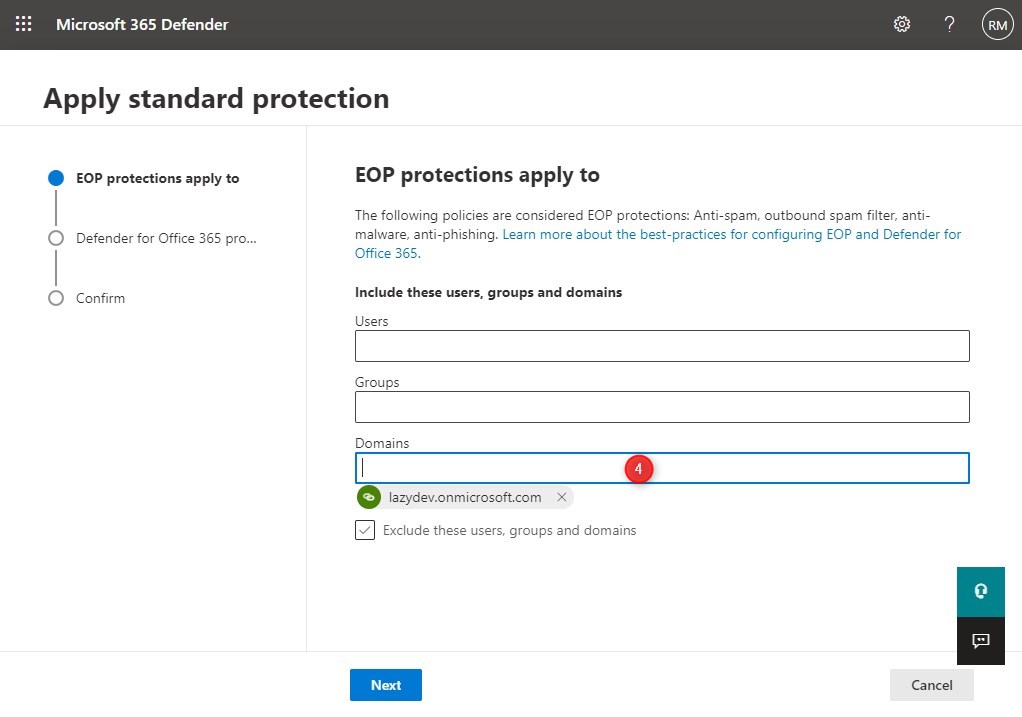
- If you
- If you have Defender for Office 365 (not included in every plan), then enable it as well for the entire domain.
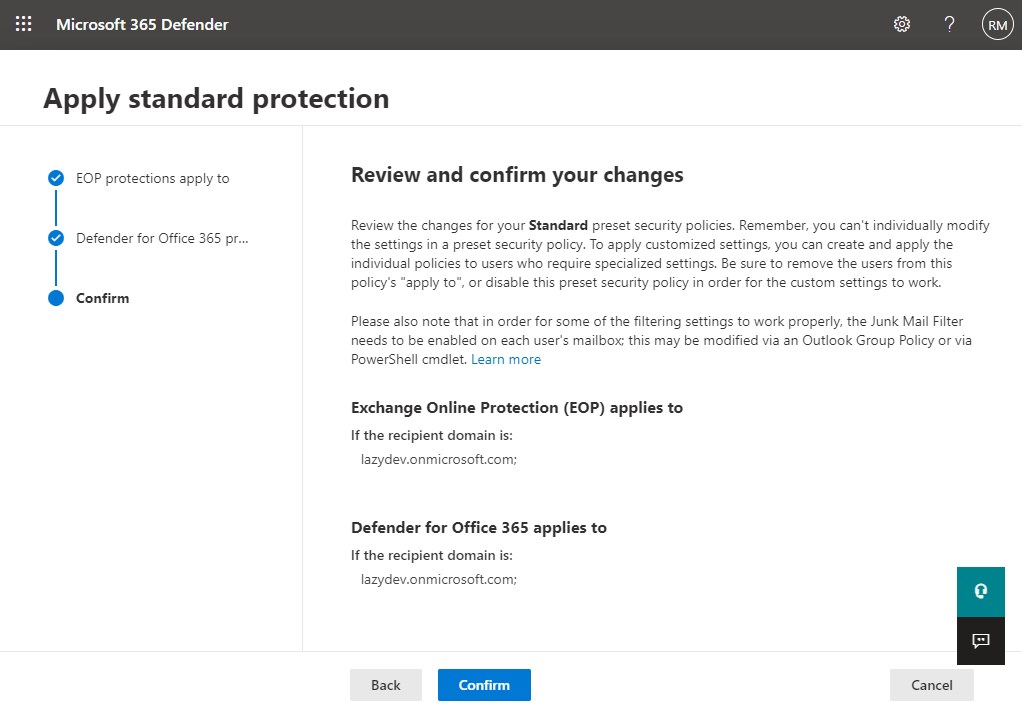
- Review your setting and click Confirm to apply the new policy.
Configuration Analyzer
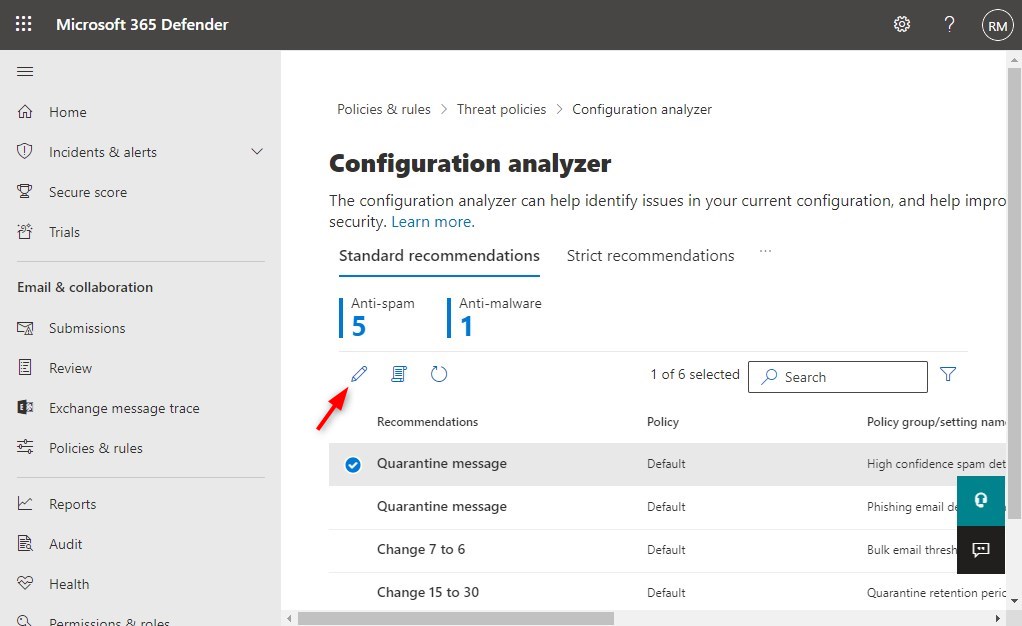
If you don’t want to use the preset security policies, then another good starting point is the Configuration Analyzer. It identifies issues with your current policies and allows you to easily change/update your settings.
- Select Policies & Rules > Threat Policies > Configuration analyzer
- Choose between Standard and Strict recommendations
- Select a recommendation to view either the policy or to apply it.
Filter common attachments
The preset policy is a good starting point, but we want to fine-tune the malware policy. You don’t want to receive emails with attachments that can contain malware, so we want to enable the common attachments filter.
This will filter out all emails with attachments like exe, docm (Word files with macro’s), reg, vbs, and more.
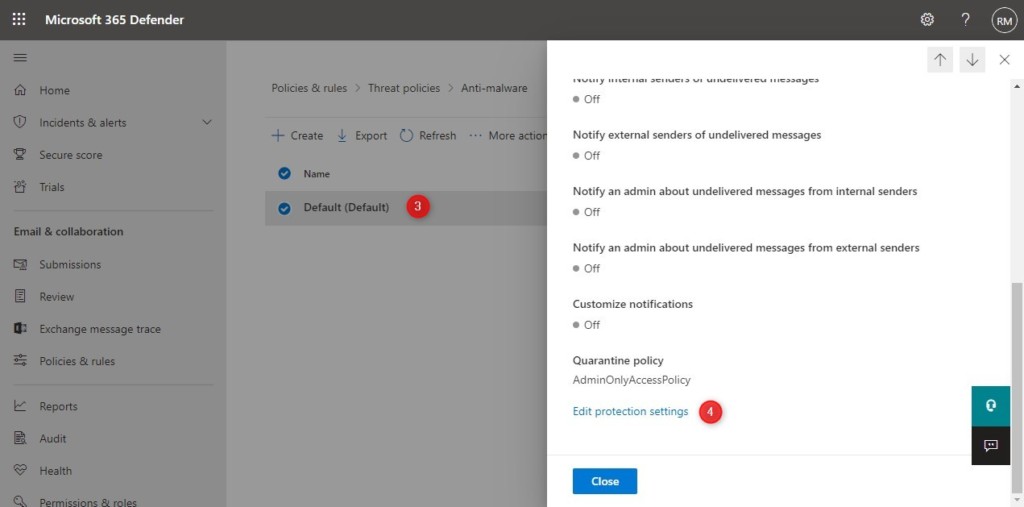
- Open Policies & Rules > Threat Policies
- Select Anti-Malware
- Click on the Default Policy
- Click Edit Protection Settings
- Enable the common attachments filter
- Click Customize file types
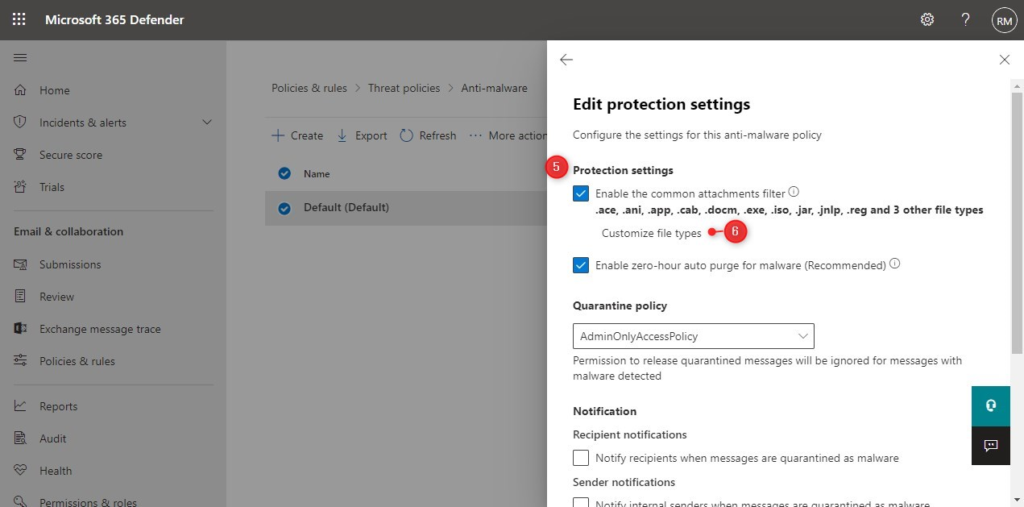
- Add at least the following file types to the default selection, and click Add at the bottom
- bat
- js
- msi
- ps1
- rar
- vb
- Enable the notifications for the recipient and internal sender. Make sure that you add a custom message to the recipient, about why the message is blocked.
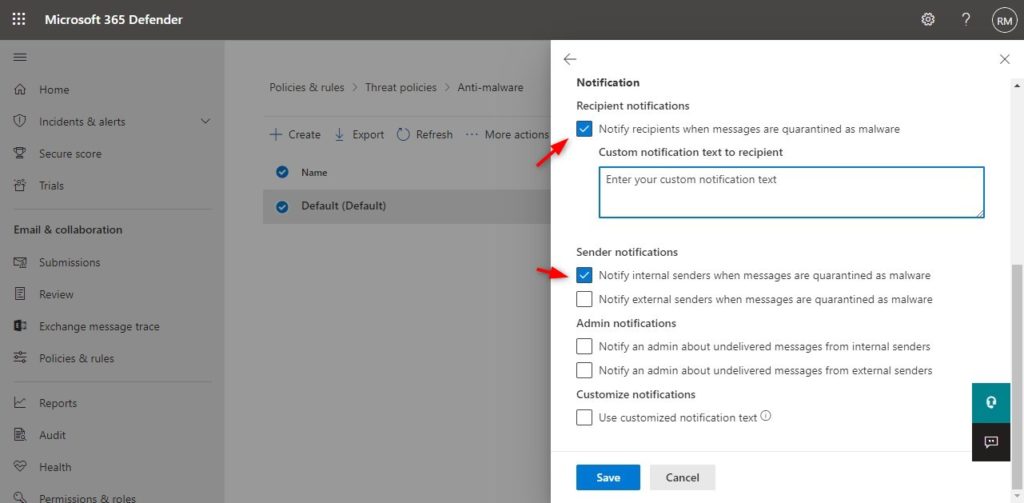
- Click save to apply the changes to the policy.
Mail flow rules
Mail flow rules allow you to apply specific rules to incoming or outgoing emails. For example, you can add a warning to potential phishing emails (based on words in the subject line or content) or warn users of potential impersonation emails.
Advanced Threat Protection
Exchange Online Protection offers good baseline protection for your mail. However, a lot of threats come from malicious links or unsafe attachments. Advanced Threat Protection (ATP) expands these security technologies and adds an extra detection tool.
ATP is part of the add-on Defender for Office 365 and is included in some Microsoft 365 plans, like Business Premium.
With Advanced Threat Protection, you get the following additional features to Exchange Online Protection.
Safe links
Safe links offer extra protection against malicious links in emails. It scans the content of the email and rewrites all URLs so that they go through Office 365. This way, they can be examined in real-time when the user clicks on the link.
The user is warned not to visit the site when the link is unsafe, and sometimes even the site is blocked altogether.
Safe attachments
With EOP, we can block attachments based on the file extension. This offers some form of protection, but Word or PDF documents can also contain unsafe content. With the safe attachments feature in Defender for Office 365, all suspicious attachments go through a real-time malware scanner.
The attachment is scanned with the use of machine learning and behavioral malware analysis for suspicious activity. Unsafe attachments are sandboxed before they are sent to recipients. This gives you better zero-day threat protection.
Reporting
Reporting helps you to get insight into who is being targeted and with what kind of threats. With reporting and the help of message trace, you can track blocked messages and see which malicious links in the message have been clicked.
Defender for Office 365 Alternative
Defender for Office 365 Plan 1 can really help bring your mail protection to the next level. But it does require additional licenses for most users, and you need to keep up to date with the configuration options.
Microsoft often releases new features that are not enabled by default on existing tenants. That means that you will need to keep track of the changes and enable new features yourself or make the required policy changes.
365 Total Protection Enterprise from Hornetsecurity offers a complete solution for only a fraction more per month. It not only reliably filters your email, but also offers tools like 10-Year Email Retention, Discovery, Email Signatures and Disclaimers, Archiving, and much more.
Another advantage of these kinds of tools is that they are managed for you when it comes to security. You don’t need to optimize the policies yourself or enable new features. They take care of it for you.
Wrapping Up
Keeping your mail free of phishing emails and malware is important. Successful phishing attempts can lead to ransomware infection—and we all know the severe consequences of a ransomware attack.
So make sure that you keep your Exchange Online Protection policies up to date and secure enough to filter out malicious emails. If you don’t want to worry about policies then take a look at third-party alternatives, like 365 Total Protection.