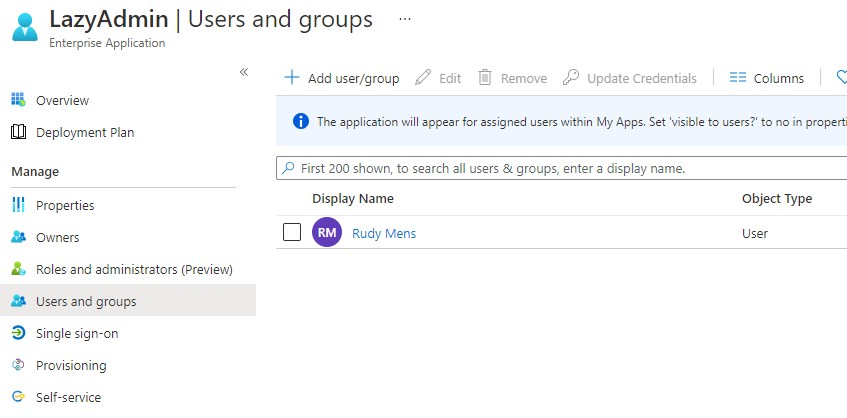
Azure AD Enterprise Applications are a great way to connect third-party applications to your Azure Active Directory. Depending on your Azure AD plan you can assign either single users to an application or complete groups.
With Azure AD Plan 1 you can only assign users, not groups. So keeping your list with users up-to-date is a hideous task. Every time you add a new user to your Office 365 tenant you will need to add the user to the Azure AD application as well.
For example, if you want to integrate Jira Cloud with Azure AD. If you have Jira Cloud Access (Atlassian Cloud Access), you can connect it with your Azure Active Directory so that new users are automatically added to Jira.
Add users to Azure AD Application with PowerShell
To automatically assign new users to enterprise applications, we need to know the existing users and all the licensed users in our tenant.
Getting licensed users is easier with Msol services, but I want to run this script in an Azure Runbook. Authenticating Azure AD is a lot easier (and more convenient) than Msol services.
Tip
If you want to know more about getting started with Azure Runbooks or Authentication in Runbooks, then make sure you read this article.
We are going to need the object id of the Azure AD Enterprise Application, the service principal to be exact. To get this, we can simply filter the AzureADServicePrincipal on the name of the application.
# Connect to Azure AD Connect-AzureAD # Get the service principal for the app you want to assign the user to $servicePrincipal = Get-AzureADServicePrincipal -Filter "Displayname eq 'APPLICATION-NAME'"
With the servicePrincial we can get all the users that has been assigned a role to the application:
# Get all users that are already assigned to the application $existingUsers = Get-AzureADServiceAppRoleAssignment -all $true -ObjectId $servicePrincipal.Objectid | select -ExpandProperty PrincipalId
We only want to add Office 365 users that have a license. If we don’t filter it, we will also get guest accounts for example.
# Get all licensedUsers
$licensedUsers = Get-AzureADUser -all $true | Where-Object {$_.AssignedLicenses} | Select displayname,objectid
The next step is to compare both lists that we have to get all the new users that we need to add:
# Compare lists
$newUsers = $licensedUsers | Where-Object { $_.ObjectId -notin $existingUsers }
So we now have a list of new users that are not assigned to the application. We can simply process this list and assign them a new role to the Azure AD Enterprise application:
ForEach ($user in $newUsers) {
Try {
New-AzureADUserAppRoleAssignment -ObjectId $user.ObjectId -PrincipalId $user.ObjectId -ResourceId $servicePrincipal.ObjectId -Id $servicePrincipal.Approles[0].id -ErrorAction Stop
[PSCustomObject]@{
UserPrincipalName = $user.displayname
AppliciationAssigned = $true
}
}
catch {
[PSCustomObject]@{
UserPrincipalName = $user.displayname
AppliciationAssigned = $false
}
}
}
I always try to use a try-catch block and output the results to a custom object. This way we can easily see what the script has done.
Wrapping Up
I have used this script in an Azure Runbook. You can find the complete script here at my Github that you can use in a runbook. Authentication is based on the Run As account of the Azure Automation account. You can find more info about that here.
If you have any questions, just drop a comment below.




Hi,
It would be great if you could help me translate this script to the new Microsoft Graph Powershell.
Thank you!
Please check out this script https://github.com/ruudmens/LazyAdmin/blob/master/MsGraph/Add-UserToAzureApplication.ps1
Due to the deprecation of Azure RunAs Accounts, I have been attempting to update this RunBook for use with a Managed Identity. However, keeps throwing an error about not loading ‘IEFrame.dll’.
Am I going about this the wrong way? What should I change?
Thanks for your help!
Have you read this article?
Rudy, I have a situation where I don’t want to add all the users to the application. These are service accounts and admin accounts, indistinguishable from other users but by ObjectId. I’ve now sort of solved it with an array of those ObjectId and an extra compare. Can it be solved more ellegant?
I do it pretty much the same way. An exclusion list (Array) and an extra comparison. The only other way to solve it would be to create an extra group in your AD with only actual users, and then get the users with Get-AzureADGroupMember
I know this is an older post. What do I need to change to run this on a local server instead of Azure Runbooks?
Only the authentication part. So remove
# Get the service principal connection details
$spConnection = Get-AutomationConnection -Name AzureRunAsConnection
# Connect AzureAD
# Check if Azure is installed and connect
if ((Get-Module -ListAvailable -Name AzureAd) -ne $null)
{
Connect-AzureAD -TenantId $spConnection.TenantId -ApplicationId $spConnection.ApplicationID -CertificateThumbprint $spConnection.CertificateThumbprint | Out-null
}else{
Write-Error "Please install AzureAd."
}
And just log in manually to azure ad
Thank you for your insight into this! This simple script will save our client thousands in Azure licensing costs.
I used a runbook just like you recommended and it works great.
What part would I have to change to assign new users to a Microsoft Team automatically in the same way?
Thanks!
You will need to use the Add-TeamUser cmdlet for this.
Would this be simple enough to switch to a list of group names in a CSV?
If Get-AzureADServiceAppRoleAssignment also returns the group PrincipalId’s then you should be able to compare that against a CSV list with Import-CSV. Maybe combine it with Get-AzureADGroup to get the group object id.
Hi Rudy,
Thanks for this guide. This is really helpful. But I’m just wondering how can we assign from .csv file?
Replace the $licensedUsers with :
# Or use CSV File
$csvUsers = Import-Csv -Path C:\temp\azuread.csv
$users = @()
$csvUsers | ForEach {
$name = $_.name
$users += Get-AzureADUser -Filter "DisplayName eq '$name'" | select ObjectId
}
And then compare:
# Compare lists
$newUsers = $users | Where-Object { $_.ObjectId -notin $existingUsers }
Here is another scenario I am wondering about. What are the possibilities currently for automating the provisioning of an Azure AD account FROM a Jira ticket? (eg., HR creates a request for new employee onboarding and a new user must be created in Azure AD).
Well, you could create a Power Automate flow, that is triggered by the Jira trigger “When a new issue is created”. And then create an Azure Automation job that runs a PowerShell script.
Maybe a good idea to built in a approval request, so you can check the request before the user is created
Thank you very much!
Hi,
can you help me to assign only Users with E3 Licenses to one of the Azure Enterprise Applications?
With this command I can get my Users with E3 Licencse:
Get-MsolUser | Where-Object {($_.licenses).AccountSkuId -match “ENTERPRISEPACK”}
Thanks
Max
You can simply replace this line with:
$licensedUsers = Get-AzureADUser -all $true | Where-Object {$_.AssignedLicenses} | Select displayname,objectid# Replace with
Get-MsolUser | Where-Object {($_.licenses).AccountSkuId -match “ENTERPRISEPACK”} | Select displayname,objectid
Hi,
exactly what I looked for. So with a Azure AD Plan 1 only there is no other way than Powershell to automate user assignment e.g. via Azure AD configuration?
Thanks Mario
Yes, that is correct.