Domain controllers are a vital part of your network. To protect them you should make sure that the firewall is enabled and only the required ports for your Domain Controller are opened. But which ports are those?
The primary function of the domain controller is of course the Active Directory. For the clients to be able to communicate with the AD, some ports need to be opened in the firewall.
In this article, we will look at which ports are required for the domain controller.
Domain Controller Ports
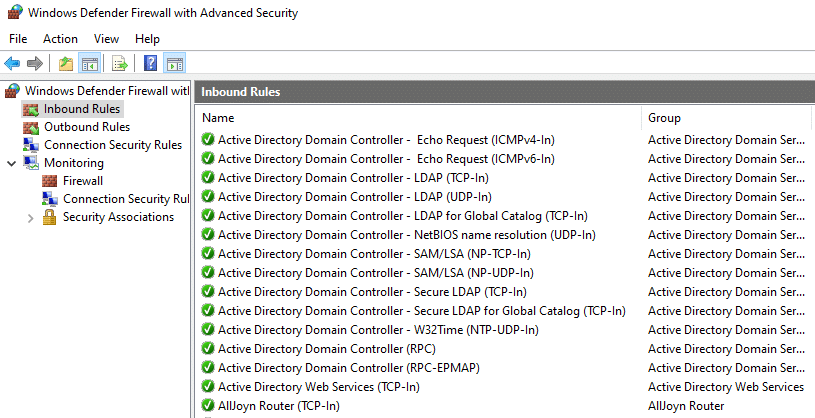
The Windows firewall is configured automatically when you install a new Domain Controller. All the required ports for your Active Directory are added automatically. But when you for example want to segment your network with VLANs, then you will need to make sure that the correct ports are open between your domain controller and clients.
Let’s first take a look at the ports that you need to open on your domain controller:
| Port | Protocol | Service |
|---|---|---|
| 53 | TCP/UDP | DNS |
| 88 | TCP/UDP | Kerberos authentication |
| 123 | UDP | W32Time |
| 135 | TCP | RPC Endpoint Mapper |
| 137/138 * | UDP | NetBIOS |
| 139 * | TCP | NetBIOS |
| 389 | TCP/UDP | LDAP |
| 445 | TCP | SMB |
| 464 | TCP/UDP | Kerberos password change |
| 636 | TCP | LDAP SSL |
| 3268/3269 | TCP | LDAP Global Catalog / LDAP GC SSL |
| 49152-65535 | TCP | RPC Ephemeral Ports |
* If you are running Windows 2012 or higher, then the NetBIOS ports are not required anymore. Netbios is replaced with SMB (Samba).
If you plan to use the Active Directory PowerShell module or the Active Directory Administrative Center, then you will need to make sure that port 9389 is opened as well.
Tip
Make sure you checkout my Domain Controller Health reporting script as well.
The RPC Port range of 49152-65535 is needed for the communication between the clients and the domain controller. The port number is randomly assigned to the client. It’s possible to limit the range through a registry key, but it’s really not recommended to do this because it might break more than you want.
Port 53 – DNS
Domain Name System (DNS) communication takes place over TCP and UDP port 53. DNS resolution is critical for domain controller location and name resolution.
Port 88 – Kerberos
Kerberos is an authentication protocol used by Windows. It operates on TCP and UDP port 88. It’s essential for secure authentication within the domain.
Port 123 -W32Time
While not directly related to domain controller operations, port 123 plays a crucial role in maintaining the synchronization of time across a network. Accurate timekeeping is essential in IT environments, especially in Active Directory, as it ensures consistent and secure authentication and access control.
Port 135 – RPC Endpoint Mapper
Port 135 is a critical client/server port used by numerous Microsoft services. In this process, the client initially connects to the RPC mapper service on port 135 to determine the dynamic port range on which the desired service is listening. The RPC mapper then responds with the port information, allowing the client to establish a connection.
Port 389 – LDAP
Lightweight Directory Access Protocol (LDAP) operates on TCP and UDP port 389. It’s used for basic LDAP queries and directory updates. LDAP is the backbone of Active Directory, facilitating user authentication and directory lookups.
Port 445 – SMB
Port 445 is used for the SMB Protocol. It’s used by the Active Directory to get GPO information. Besides that, the protocol is also used for file and printer sharing.
Port 636 – LDAP
For enhanced security, LDAPS (LDAP over SSL) operates on TCP port 636. LDAPS encrypts the data transmitted between domain controllers, safeguarding sensitive information.
Port 3268/3269 – LDAP Global Catalog
The ports 3268 and the secure version 3269 (which uses SSL) are used for querying the LDAP Global Catalog.
Port 49152-65535 – RPC Ephemeral Ports
A port in this range is allocated to the client after the initial contact with the RPC Mapper on port 135.
ADFS Ports
If you are using Active Directory Federations Services (ADFS), then you will need to make sure that the following ports are open as well:
| Port | Protocol | Service |
|---|---|---|
| 80 | TCP/UDP | HTTP |
| 443 | TCP/UDP | HTTPS |
| 5985 | TCP/UDP | WinRM Listener |
| 49443 | TCP | Active Directory Federations Services (ADFS) |
Port 5985 is needed when using Azure AD Connect or Federation/WAP servers. Port 49443 is needed for ADFS when using certificate-based authentication.
Wrapping Up
The Windows Firewall on your domain controller is configured correctly by default when you install the Active Directory services. If you are using a third-party firewall on your domain controller, or planning to use VLANs, then you will need to make sure that the listed ports are opened.
As mentioned, NetBIOS ports are not really needed anymore, so it’s better to block them if you don’t have any apps that use them.
I hope you found this article helpful, if you have any questions, just drop a comment below.



Important notification:
The ports should be opened on the LAN network only, not WAN!
When clients need to connect to the Domain Controller, DC, from a different location over the internet, they should access the network through VPN first.
in beginning of this page is many times UPD – but its UDP not UPD 🙂
Well, if I make a typo, I atleast be consitent with it :). Thanks!